Digitizing is “just” a change…
Digital transformation is labeled as a new Industrial Revolution and it seems that if you do not digitize your plant you are out of date. The market is going to stretch us more than we need, but we have to be true to our vision and be conservative. As the great cybersecurity guru Patrick Miller says, “before you set an alarm, you close the windows.” One of the first “windows” that we have to close is to ensure that we all take cybersecurity into account on a day-to-day basis. It is a difficult change to implement, because we will all accept a change to “digital” that provides benefits, but if that change to “digital” is associated with annoying considerations, cybersecurity becomes the less friendly face of digitization.
Analog is safer…
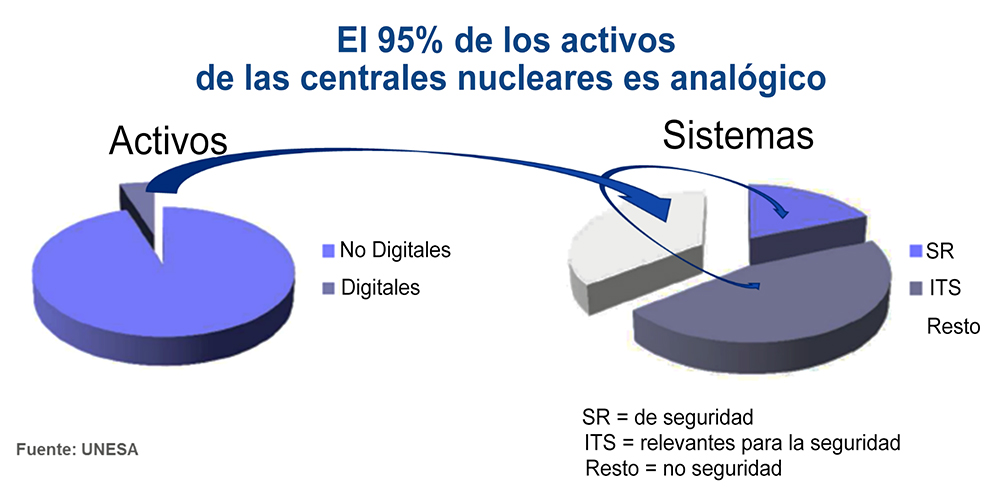
A failure in a digital system has the same impacts in your bussiness as that failure in its analog counterpart and also the same nature of threats. However, a digital system has a set of vulnerabilities that “cyberattacks” exploit. But basically, the safest system will be the one in which your Security is managed most effectively. In our plants we have something differentiating: 95% of the assets of a plant are analog, and these are concentrated in Non-Important to Safety Systems. So we have the “nuclear analogue paradox”, the classic analogue nuclear design gives us an advantage over modern plants. For this reason, it is important to maintain the “core” of Important Safety Systems in their analog design.
Cybersecurity by design
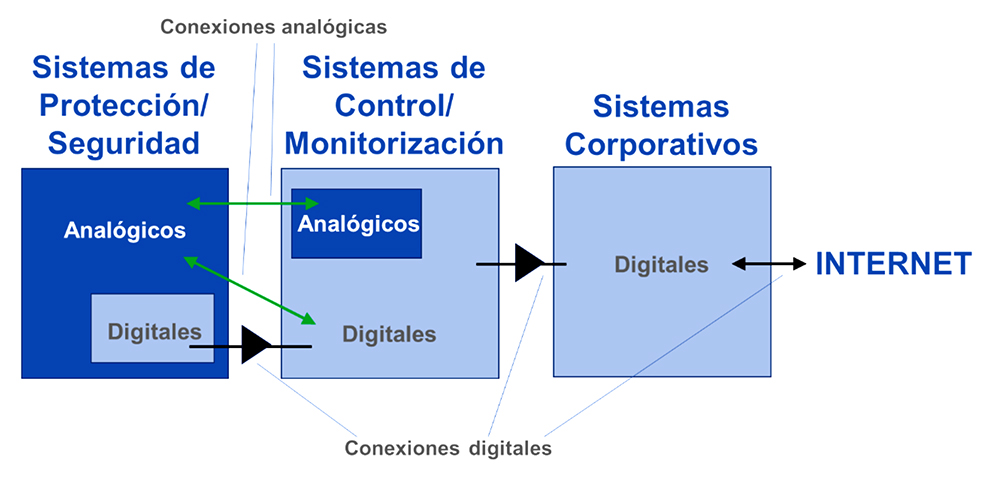
For a digitization project to be successful, it is essential to design with the Cybersecurity by default. In Spanish plants there is a complete digital isolation of nuclear security and physical security systems, as a requirement of the CSN in 2012. In the field of monitoring and control systems, we have more volume of digital assets to protect. An effective method is to include a second isolation with corporate networks, where we emphasize the protection of personal data and the external border, without using cloud services that we need in case we isolate ourselves from the internet.
Maintenance of cybersecurity
When implementing a new system or digital assets, it is essential to generate its maintenance procedures in parallel, including, among others, insider mitigation rounds and log extraction. Joining efforts we managed to generate the appropriate designs that facilitate the execution of the precise maintenance tasks, so that the system is prepared to undertake a complete cybersecurity audit and have tools for detection and response to incidents.
Incident response and creative nuclear professionals.
It is a requirement of the Law that we have mechanisms to detect, respond and report cybersecurity incidents. We report in a format according to the casuistry of the incident. It is more difficult to detect, because we need data to analyze and the bad guys will try not to leave a trace. And the most complicated thing is to respond. The big problem with cybersecurity is that it is not possible to process all defense actions, because we do not know what new weapons attackers will use, nor are unpublished rulings known.
To respond to an incident, we must be able to find solutions to unknown problems, but also other approaches to known problems.